|
Listen Now
Getting your Trinity Audio player ready...
|
- The Burning Question in Every Boardroom
- How AI Quietly Walked Through The Front Door
- The Dropbox Toggle That Sparked A Global Backlash
- The WhatsApp Problem: A $9.2 Billion Wake-Up Call
- The Document That “Refuses To Download
- The DPDP Act Changes Everything
- When The Cloud Itself Fails: Silent Data Corruption And Lockouts
- Enter MaMITs DMT: A Self-Hosted, Made-in-India Answer
- Zero Third-Party Dependencies
- Military-Grade Encryption
- Secure Sharing Without WhatsApp
- DPDP Act Compliance, Built-In
- Backup, Recovery, And No 30-Day Lockouts
- How It Compares
- The Verdict From The Field
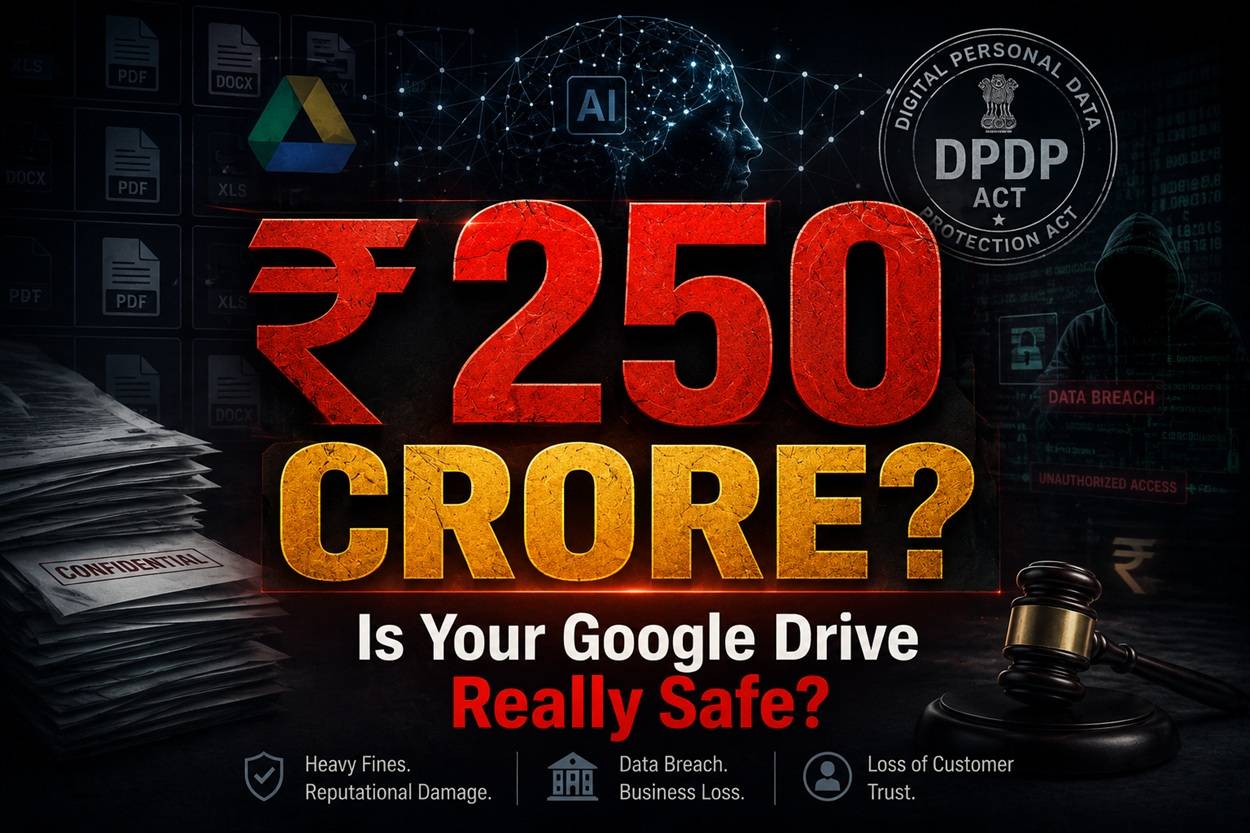
BHOPAL, May 14: A quiet panic is spreading through corner offices across India. The question being whispered in board meetings, WhatsApp groups of CEOs, and late-night calls between founders and their CTOs is deceptively simple: Is the document I just uploaded to Google Drive being used to train someone’s AI model?
For years, the answer felt obvious. Cloud storage was supposed to be the digital equivalent of a bank vault Google, Microsoft, and Dropbox were the institutions guarding the keys. That assumption is now in tatters. A combination of opaque terms-of-service updates, the unchecked rise of generative AI inside enterprise productivity suites, India’s newly enforceable Digital Personal Data Protection (DPDP) Act, 2023, and the sheer technical fragility of consumer-grade tools like WhatsApp, has forced a reckoning.
And the cost of getting it wrong is no longer reputational. It is existential. Under the DPDP Act, a single security lapse can trigger a penalty of up to ₹250 crore — an amount that can wipe out a mid-sized Indian company overnight.
Against this backdrop, Bhopal-headquartered MaMITs Pvt. Ltd. has launched MaMITs DMT, a self-hosted document management system pitched as India’s answer to a global crisis of data sovereignty. The product, the company says, is built on a single conviction: in the age of AI, the only document that is truly safe is the one your business and only your business controls.
The Burning Question in Every Boardroom
Speak to any founder in Indore, Bengaluru or Gurugram today and the conversation eventually turns to the same anxiety. A senior product head at a Bhopal-based logistics firm, who asked not to be named, put it bluntly: “I have eight years of client contracts, GST invoices and HR records sitting on Google Drive. Last week our compliance officer asked me if I could prove — prove — that none of it has been seen by an AI model. I couldn’t.”
He is not alone. According to industry estimates, the global Document Management System (DMS) market is projected to reach $25.05 billion by 2032, growing at a compound annual rate of 15.9 per cent. The Asia-Pacific region is racing ahead at a CAGR of 18.43 per cent, driven largely by India’s Digital India push and the rapid digitisation of small and medium businesses. The migration is enormous. The scrutiny, until recently, was minimal. That has now changed.
How AI Quietly Walked Through The Front Door
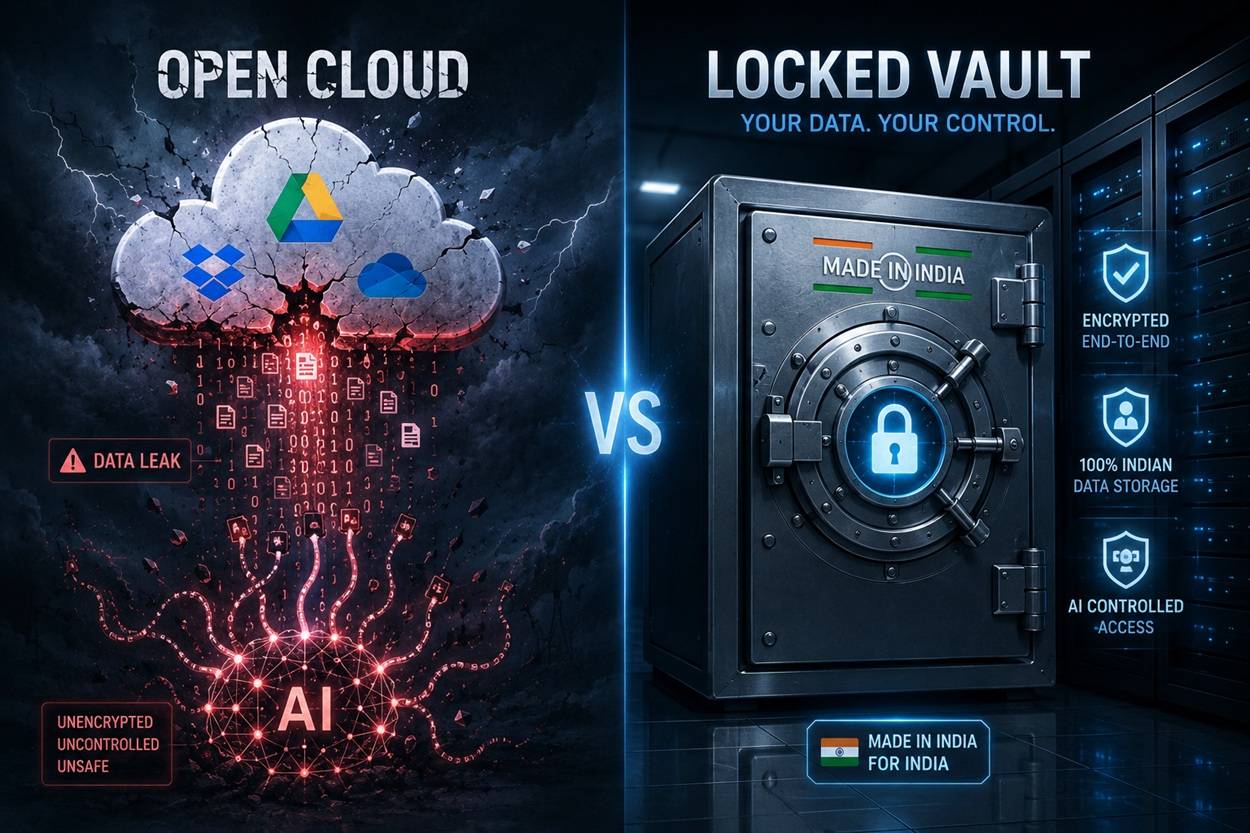
The first crack appeared with the integration of generative AI directly into the platforms that businesses trust. Google’s Gemini, Microsoft’s Copilot, and Dropbox AI did not arrive as separate products. They arrived as features switched on by default, woven into the same drives, mailboxes and shared folders that hold a company’s intellectual property.
What changed, security researchers say, is not just access. It is amplification.
In a traditional cloud environment, an overshared file say, a payroll spreadsheet accidentally set to “anyone with the link” was a dormant risk. An attacker had to know it existed. Generative AI removed that friction. Modern enterprise AI tools index entire repositories. An internal user can now retrieve sensitive HR data, source code, or financial projections simply by typing a question into a chat box. According to a Better Cloud analysis cited in industry research, the threat model has shifted overnight from “can someone breach the perimeter” to “can an employee retrieve confidential data simply by asking the AI.”
Worse is the phenomenon now known as Shadow AI employees connecting unapproved tools like ChatGPT, Claude or third-party browser plugins to corporate drives via OAuth permissions. A staffer who only wants to summaries one document may unwittingly grant a third-party LLM read-write access to an entire Google Drive. By default, several consumer-facing AI services use those inputs to train their next-generation models unless users explicitly opt out — a setting most users have never seen.
OpenAI’s own documentation acknowledges that user data may be used to improve its models, with opt-out buried inside account settings. A Stanford HAI report warned that uploads to popular chatbots like ChatGPT and Gemini may end up in training datasets unless the user actively disables the option.
The Dropbox Toggle That Sparked A Global Backlash
The single moment that crystallised public fear came in December 2023, when Dropbox users discovered a new default setting that allowed personal data to be shared with third-party AI companies, including OpenAI. The toggle was on by default. The backlash was severe. Dropbox’s CEO insisted that third-party AI services were only used when customers actively engaged with the features — but the very fact that the option had been pre-enabled triggered an uproar among enterprise customers and privacy advocates.
The damage compounded. In April 2024, Dropbox Sign (formerly HelloSign) suffered a security breach in which attackers entered the production environment and obtained sensitive user data and authentication tokens. For businesses that had treated Dropbox as a digital filing cabinet, the message was unmistakable: trust, once defaulted, is hard to reclaim.
Other platforms have stumbled too. Dutch file-sharing service WeTransfer quietly updated its terms in 2025 to grant itself a “perpetual, worldwide, royalty-free” licence to use uploaded files for developing machine-learning models. The clause was retracted within days after creative professionals revolted on social media. Adobe faced a similar storm over wording that suggested user content could feed AI training.
Google maintains that Workspace data is exempted from base-model training by default. Microsoft says Copilot prompts and responses are not used to train foundation models. Both statements are technically accurate. Both also rest on a layer of default settings “smart features,” sub-processors, regional data boundaries that ordinary administrators struggle to interpret. A May 2024 update to Google’s Terms of Service triggered fresh confusion among Workspace admins, with users in Google’s own support forums asking how to disable AI features for their entire organization.
The pattern, security experts argue, is structural. When a business stores documents on a multi-tenant public cloud, it is permanently exposed to unilateral changes in the terms of service. The fear that intellectual property is being used, in some form, to train someone’s AI is not paranoia. It is a rational reading of how the architecture works.
The WhatsApp Problem: A $9.2 Billion Wake-Up Call
If the cloud is one front in this war, WhatsApp is the other.
India is the world’s largest WhatsApp market with more than 620 million users, who together spend an average of 17 hours a month on the app. Somewhere along the way, the green-tick messenger turned into the country’s de facto business infrastructure. Quotations, contracts, GST documents, design files, HR letters, even patient prescriptions all routinely travel through chats originally designed for personal use.
The compliance cost has been staggering. In 2023 alone, the US Securities and Exchange Commission and the Commodity Futures Trading Commission levied fines totalling $9.2 billion on financial institutions for messaging-related compliance violations. JPMorgan and Goldman Sachs paid over $2 billion combined, after regulators found their compliance teams had no oversight over employees conducting business on unauthorised, “off-channel” applications.
A 2024 Deloitte survey cited in industry reporting found that only 38 per cent of organizations using messaging apps have formal policies in place to ensure compliance with data privacy regulations. Even more striking: while 59 per cent of compliance teams have attempted to ban WhatsApp for business use, only 2.6 per cent are confident the bans are effective. The practice, regulators concede, simply goes underground.
End-to-end encryption, often cited as WhatsApp’s safety net, applies only to messages in transit. The backups stored on Google Drive, iCloud, or the device’s own memory are frequently unencrypted. If a phone is lost, stolen, or sold without a factory reset, the entire history of business documents can be exposed. WhatsApp’s global directory model, where any user can contact any other, also widens the attack surface: a malicious actor can target employees with malware-laden files in a way no closed enterprise system would allow.
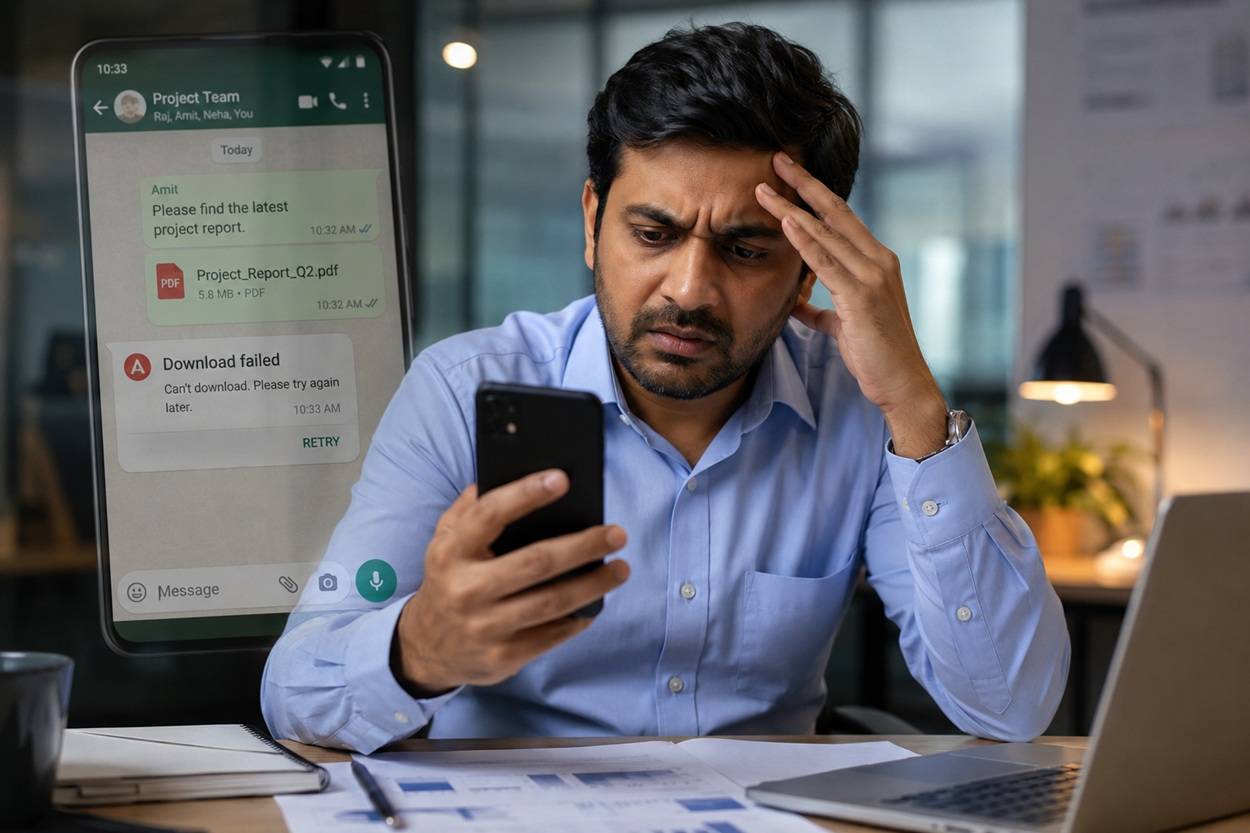
The Document That “Refuses To Download
Beyond compliance, there is a more immediate, more familiar frustration. Ask any office manager in Bhopal or Pune about the most-hated phrase in business communication, and the answer comes quickly: “The download was unable to complete. Please try again later.”
The error is not random. WhatsApp does not function as permanent cloud storage. Document download links live on Meta’s servers for a limited window — typically a few weeks — after which the file is permanently deleted. A user who tries to retrieve a three-month-old invoice often finds the link is dead, and if the original sender has cleared their phone, the document is gone for good.
Other failure modes compound the problem. Devices with less than 3GB of RAM frequently freeze while loading large PDFs. Corrupted caches, read-only SD cards, and Google Play Store sync errors (codes 413, 491, 505, 907, 927) regularly block downloads on Android devices. Format incompatibility — the dreaded “this file format is not supported” — strikes whenever a sender uses a slightly newer document standard than the receiver’s reader app supports.
And then there is the worst-case scenario, the one every business owner has lived through at least once: the mobile is formatted, the chat history is gone, and the only copy of a critical contract vanishes with it. WhatsApp’s Request Account Info feature returns account settings and metadata not the lost documents. There is no recovery. There is only regret.
The DPDP Act Changes Everything
For Indian businesses, the regulatory ground has shifted permanently with the Digital Personal Data Protection (DPDP) Act, 2023, whose final rules were notified in November 2025. Full compliance is mandatory by mid-May 2027, making the current period what compliance lawyers are calling a “Build Year” the last window in which Indian companies can quietly overhaul their document infrastructure before the penalties start to bite.
The penalties are not symbolic. They are designed to terrify.
| DPDP Act Violation | Maximum Penalty | What This Means For Document Management |
|---|---|---|
| Failure to implement security safeguards | ₹250 crore (~$30 million) | Storing unencrypted customer data on shared drives or personal devices directly triggers this. |
| Failure to notify breach within 72 hours | ₹200 crore | Without tamper-evident audit logs, breach detection is impossible. |
| Children’s data violations | ₹200 crore | Failure to segregate data of users under 18 in general storage. |
| Consent Manager violations | ₹500 crore | Absence of valid data management structures. |
| Failure to fulfil Data Principal rights | ₹50 crore per instance | Inability to locate or delete specific user data on request — a near certainty with Shadow IT fragmentation. |
For most Indian SMEs and mid-sized enterprises, a ₹250 crore fine is not a regulatory speed bump. It is a closure event.
The Act also enshrines data residency as a core principle. Personal data can be transferred only to countries the central government formally notifies as offering “adequate” protection standards. The Reserve Bank of India has gone further for the financial sector, mandating that end-to-end transaction data of payment processors, fintech firms and banks must reside on infrastructure physically located within India. For companies still routing documents through globally distributed AWS regions or Google Cloud buckets in Singapore and Frankfurt, the compliance gap is widening by the day.
When The Cloud Itself Fails: Silent Data Corruption And Lockouts
Even setting AI and regulation aside, the public cloud has been quietly failing in ways that most business owners do not realise.
Silent Data Corruption (SDC) is the industry’s polite term for a problem that has haunted hyperscale data centres for years: bits in a memory chip flip without warning, a faulty RAID controller mutates a single byte, a cache flush bug rewrites a file — and the system reports nothing. Gartner estimates that 20 per cent of mission-critical applications experience some form of data corruption every year. The Ponemon Institute attributes more than 75 per cent of all data-loss incidents to a combination of software corruption, hardware error and human mistakes. Veeam’s research found that 82 per cent of businesses experienced at least one unplanned outage in a single 12-month period, with corruption acting as a primary catalyst.
The deepest irony of modern cloud storage is that its core defence instant replication across multiple data centers — actively destroys clean copies of corrupted files. When a database row or a critical PDF is silently mutated, the synchronisation engines obediently copy that corrupted state to every backup node before any administrator notices.
Then there are the lockouts. Stories pile up in support forums of businesses logging into their Google Workspace admin console one morning to find the entire workspace suspended — emails bouncing, drives inaccessible, audit logs sealed off. The triggers are mundane: a failed payment, a false-positive security flag, an automated billing dispute. The consequences are not. Recovery commonly takes up to 30 days, during which operations grind to a halt. Because hyperscale platforms lack dedicated, human-in-the-loop support for smaller customers, owners are forced through automated forms, DNS verification routines, and community-forum SOS posts.
When the infrastructure is leased rather than owned, sovereignty is an illusion.
Enter MaMITs DMT: A Self-Hosted, Made-in-India Answer
It is into this landscape that MaMITs DMT — short for Document Management Tool — has been launched. The product, developed by MaMITs Pvt. Ltd. from its Bhopal headquarters, is positioned not as another SaaS subscription but as a structural alternative to the entire public-cloud model.
The company’s core claim is simple: in a world where every major platform has, at some point, defaulted users into AI training or surveillance, the only credible defence is to own the infrastructure outright.
Zero Third-Party Dependencies
MaMITs DMT runs entirely on the enterprise’s own servers, whether on-premises or on a privately leased instance. The software, the company says, does not connect to external APIs, does not phone home to Silicon Valley, and does not share metadata with web scrapers or cloud AI agents. Documents stay where they are placed.
Military-Grade Encryption
Every document ingested into the system is encrypted at the column level using AES-256-GCM (Galois/Counter Mode) — the same standard relied on by defence agencies, financial regulators and zero-knowledge security vendors. The mode provides both confidentiality and message authentication, meaning a tampered file is detectable. Even in the event of a physical server breach, the raw database files are unreadable.
Secure Sharing Without WhatsApp
To replace the WhatsApp-and-email habit, the system generates secure share links protected by password, expiry dates and view limits. A vendor can no longer sit on a confidential RFP file forever; a former employee cannot forward an old contract from a personal device. Strict role-based access control draws clear walls between Admins, Uploaders and Viewers. A “strict uploader lockout” role prevents staff from modifying or deleting files post-upload — closing a common audit hole.
Access is fortified by Time-Based One-Time Password (TOTP) two-factor authentication compatible with Google Authenticator and similar apps, neutralising the credential-stuffing attacks that plague ordinary email and messenger logins.
DPDP Act Compliance, Built-In
Because the system is self-hosted and “Made in India”, organisations can deploy it strictly within domestic data centres — closing the cross-border transfer gap that the RBI and DPDP Act have flagged as a serious risk. A tamper-evident, hash-chained audit log records every document interaction cryptographically, giving compliance officers the breach-notification evidence the law now demands within 72 hours. Ten customisable metadata fields, paired with automated renewal alerts at 7, 30 and 90 days, allow companies to automatically retire documents at the end of their legal retention period — a key requirement of the DPDP Act’s data-minimisation principle.
Backup, Recovery, And No 30-Day Lockouts
Because the enterprise owns the infrastructure, the spectre of an algorithmic 30-day account suspension simply disappears. The system supports one-click full backups with a triple-layer restore mechanism, and its offline-to-online sync — secured by HMAC authentication — allows operations to continue during localised network outages without versioning conflicts. A built-in USB scanner integration (Canon, HP, Epson) bridges physical and digital workflows for businesses still moving away from paper.
How It Compares
| Capability | General Cloud (Drive, Dropbox) | Shadow IT (WhatsApp, Email) | MaMITs DMT |
|---|---|---|---|
| Data residency control | Poor — globally distributed | Zero — Meta servers and third parties | Complete — self-hosted |
| AI training exclusion | Ambiguous; opt-out required | High risk; metadata scanning | Guaranteed; zero dependencies |
| Encryption standard | At rest; provider holds keys | In transit only; backups unsecured | AES-256-GCM at column level |
| Expiring share links | Partial, subscription-tied | Not available | Yes, with password and view limits |
| Audit logging | High-tier subscriptions only | Non-existent | Tamper-evident, hash-chained |
| Account lockout risk | High — algorithmic suspensions | High — device loss, bans | Zero — owned infrastructure |
| Pricing | Recurring monthly SaaS | “Free” — monetised via data | Free Forever core tier |
The “Free Forever” core tier is a deliberate strategic choice, the company says. The intention, according to MaMITs leadership, is to remove the cost barrier that has historically pushed small Indian businesses into the very Shadow IT habits the DPDP Act now penalises.
The Verdict From The Field
Independent observers of India’s data-protection landscape say the shift away from public cloud for sensitive document workloads is no longer a question of whether but when. “The DPDP Act doesn’t punish you for using Google Drive,” one Delhi-based data-protection lawyer noted. “It punishes you for being unable to prove what happened to a document, who saw it, when it was deleted, and where it was stored. The cloud model is structurally weak on every one of those questions.”
For business owners, the calculus is starting to look different. A monthly Workspace subscription that once seemed cheap now reads as a recurring exposure to AI training risk, vague terms-of-service updates, foreign data residency, and a 30-day lockout always one billing dispute away. A self-hosted system, by contrast, demands more from the IT team — but returns something that the cloud era had taught everyone to live without: ownership.
The Bhopal-based company is betting that ownership, in 2026, is no longer a luxury. With AI models hungry for training data, regulators armed with ₹250 crore penalties, and WhatsApp groups still humming with confidential contracts, the question facing every Indian business has become harder to dodge.
Is your document really safe?
For a growing number of founders, the honest answer is that they do not know — and that the price of finding out the hard way is now too high to pay.
About MaMITs DMT: MaMITs DMT is a self-hosted document management system developed by MaMITs Pvt. Ltd., Bhopal. The platform offers AES-256-GCM column-level encryption, tamper-evident audit logs, role-based access control, TOTP 2FA, secure expiring share links, automated retention alerts and DPDP Act 2023-aligned data residency. More information is available at mamits.com/dmt-document-management-system.
About MaMITs Pvt. Ltd.: MaMITs Pvt. Ltd. is a Bhopal-headquartered software company building enterprise-grade tools for Indian businesses, with a focus on data sovereignty, compliance-first design and self-hosted architecture.